This weekend Grouse Mountain opened its Screaming Eagle chairlift to the “midstation.” Normally the Screaming Eagle chair runs all the way from the bottom of the Cut to the top. The midstation is generally only used during “early season conditions,” and allows the top half of the Cut to be opened for skiing even if the bottom half does not have enough snow coverage. This winter has been particularly warm, and thus snow has been very lacking. The midstation setup consists of half of a cross-arm with supporting sheaves on Tower 7. This half-arm is only rotated in line with Continue Reading
The Sea to Sky Gondola
I last blogged about the Sea to Sky Gondola after its first incident where its haul rope was maliciously cut in the middle of the night. (It was also unfortunately cut a second time the following year, but fortunately, there have been no incidents since then.) Despite being open on the Sea to Sky since 2014, I never found the opportunity to visit the attraction. This Christmas season, Grouse Mountain gave its passholders a special perk: free admission to the Sea to Sky Gondola. This was due to a lack of snow on Grouse Mountain, where passholders would normally be Continue Reading
Replacing a failed disk in RAID on an OVHcloud dedicated server
Yesterday morning, I woke up to some Discord messages saying that one of my websites was offline. Not a great way to start off the morning! I tried to first ascertain the scope of the issue—turns out none of my services were accessible at all from that one dedicated server. Panic started to set in a bit… did I forget to pay my monthly server bill? Did the server get hacked? Or did the server burn down?
Psalm 25
Prayer for Guidance and for Deliverance. A Psalm of David.
“To thee, O Lord, I lift up my soul. …”
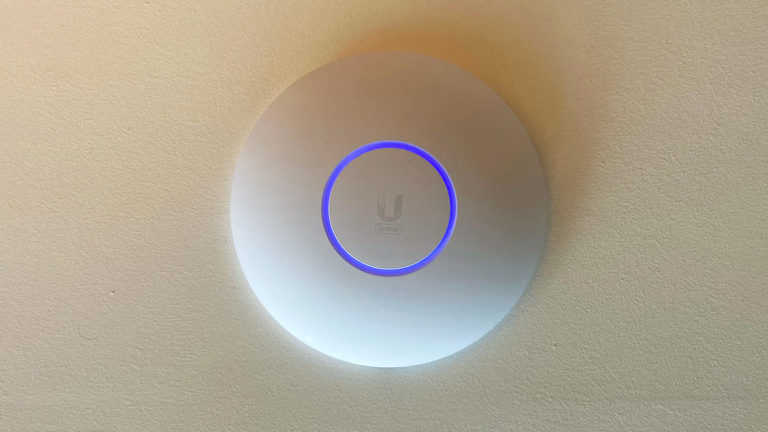
DIY: How to mount a UniFi access point to the ceiling
Last year when I moved into my new apartment, I upgraded to a Ubiquiti UniFi Dream Machine (UDM) router to support the gigabit Internet speed I could now subscribe to. Due to the location of the fiber optical network terminal (ONT) in my home, the UDM had to be located in the closet of my secondary bedroom, which is on one side of the apartment. Now while the UDM has a powerful enough Wi-Fi signal that can cover my apartment reasonably, the 5GHz band, is significantly weaker two walls over in my main bedroom. In addition, over the summer I Continue Reading